Post Mortem: PoolZ Token Vesting Contracts
Mar 16, 2023
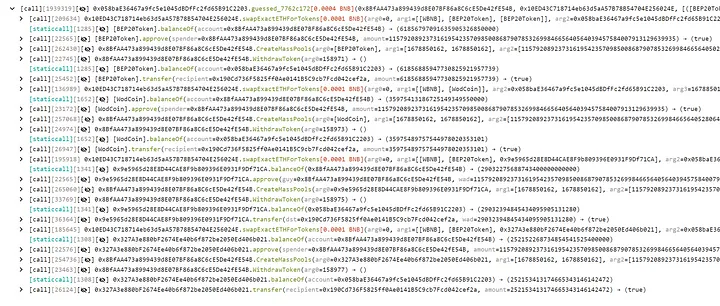
The PoolZ Token Vesting Contracts were hacked yesterday (March 15, 2023). The hack occurred at 03:16 AM +UTC on BSC, 03:09 AM +UTC on Ethereum, and 02:59 AM +UTC on Polygon. This hack was first detected by Bythos and swiftly reported upon and analyzed by the security firm, Peckshield.
The vulnerability that led to this unfortunate incident, an arithmetic overflow attack, occurred in the unaudited LockedControl.sol in the Integrate repository.
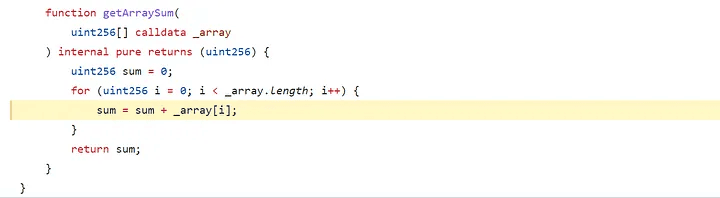
Vulnerable Code in the LockedControl.sol contract at Line #152 in PoolZ/Integrate at Latest Commit #24dd7e51efcb58cb6b649e75c4c1c3c54ec2558c
The hacker was able to utilize an overflow vulnerability in the highlighted point in the contract, by which they created multiple pools for each asset type while committing substantive assets that they did not have that cumulatively hit the cap of the token contract limit (MAX U256) overflowing it to zero thus allowing for the attacker to deposit zero while getting a credit balance for the overflow amount. This is done by the hacker calling CreateMassPools function. This then allowed the hacker to call the WithdrawToken function withdraw the assets from the created pools without having deposited the corresponding amounts.
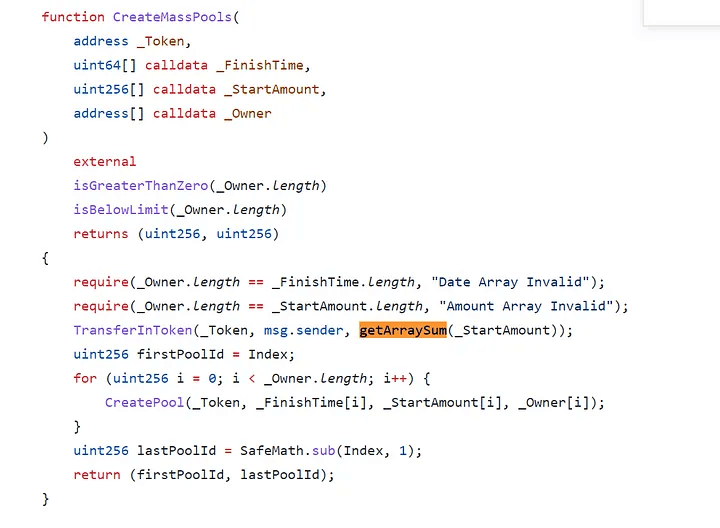
Vulnerable function in the LockedControl.sol contract that utilizes vulnerable getArraySum Function in PoolZ/Integrate at Latest Commit #24dd7e51efcb58cb6b649e75c4c1c3c54ec2558c
This vulnerability is not as easily possible in later solidity versions (the contract is written with the solidity version 0.6.0) as native overflow safeguards were added in later versions.
Other versions of this vulnerable code exist in an unaudited and currently unused array.sol . We believe this version would not be exploitable as easily due to arithmetic overflow safeguards in later solidity versions. Nonetheless, we have recommended the complete removal of that library for safety.
Our thoughts are with the PoolZ team during this challenging time, and we have made our team available to them for any assistance we may be able to provide.